The risks of open schedules
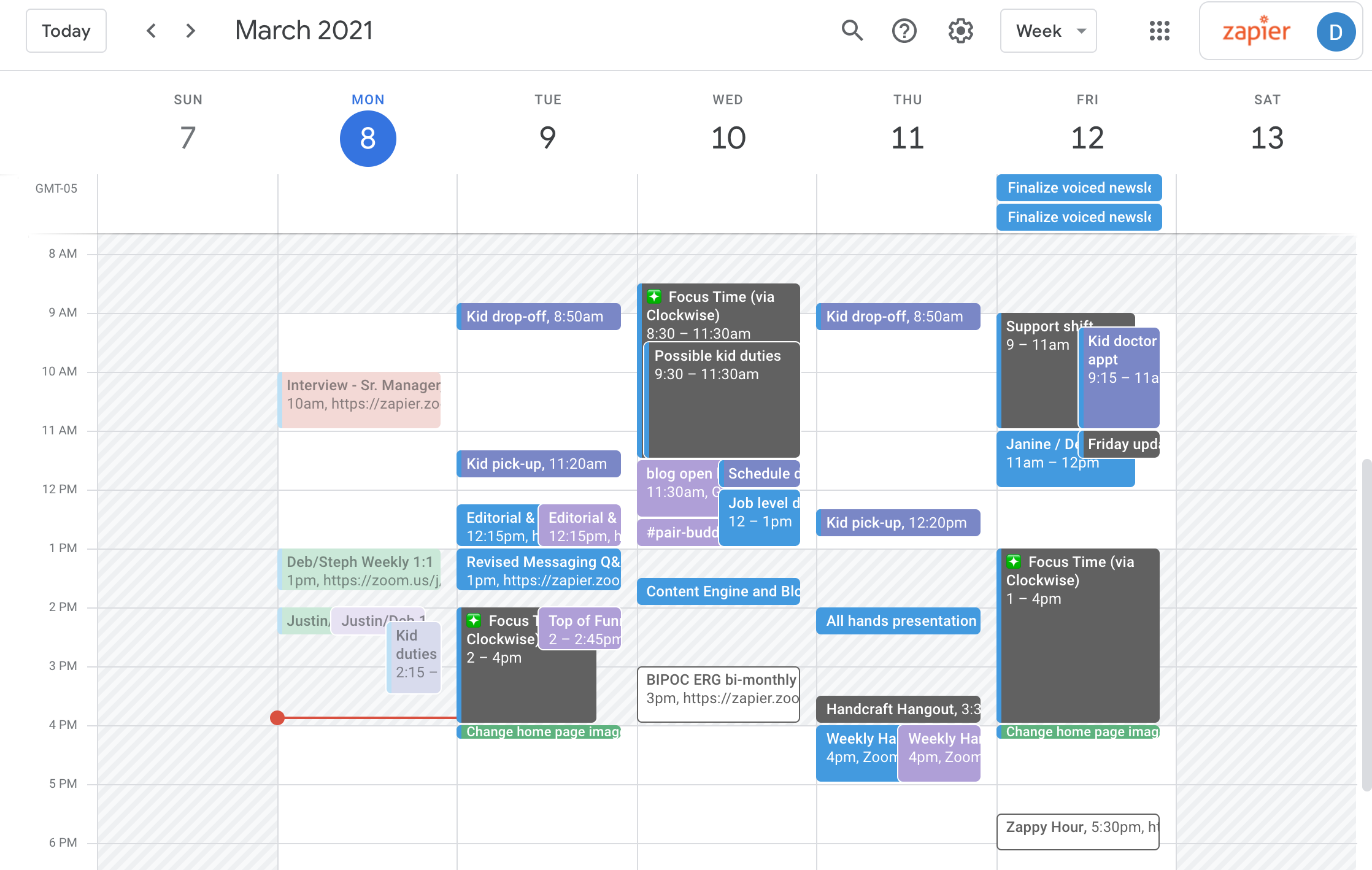
Most of us share our schedules without thinking twice. Between remote work and family coordination, our calendars are open to more people than they were five years ago. This convenience comes with a trade-off: if you don't know exactly who can see your data, you're likely oversharing your location and habits.
The risks of oversharing are real. A publicly visible calendar can reveal your location, habits, and even potential vulnerabilities. The privacy landscape is constantly evolving, with new threats and concerns emerging regularly. What felt safe a few years ago might be surprisingly open today.
This guide is designed to help you navigate these complexities. We’ll cover everything from understanding permission levels to platform-specific privacy settings, and offer practical advice for sharing calendars securely with family, friends, and colleagues. Consider this your toolkit for taking control of your schedule and your data.

Understanding Calendar Permission Levels
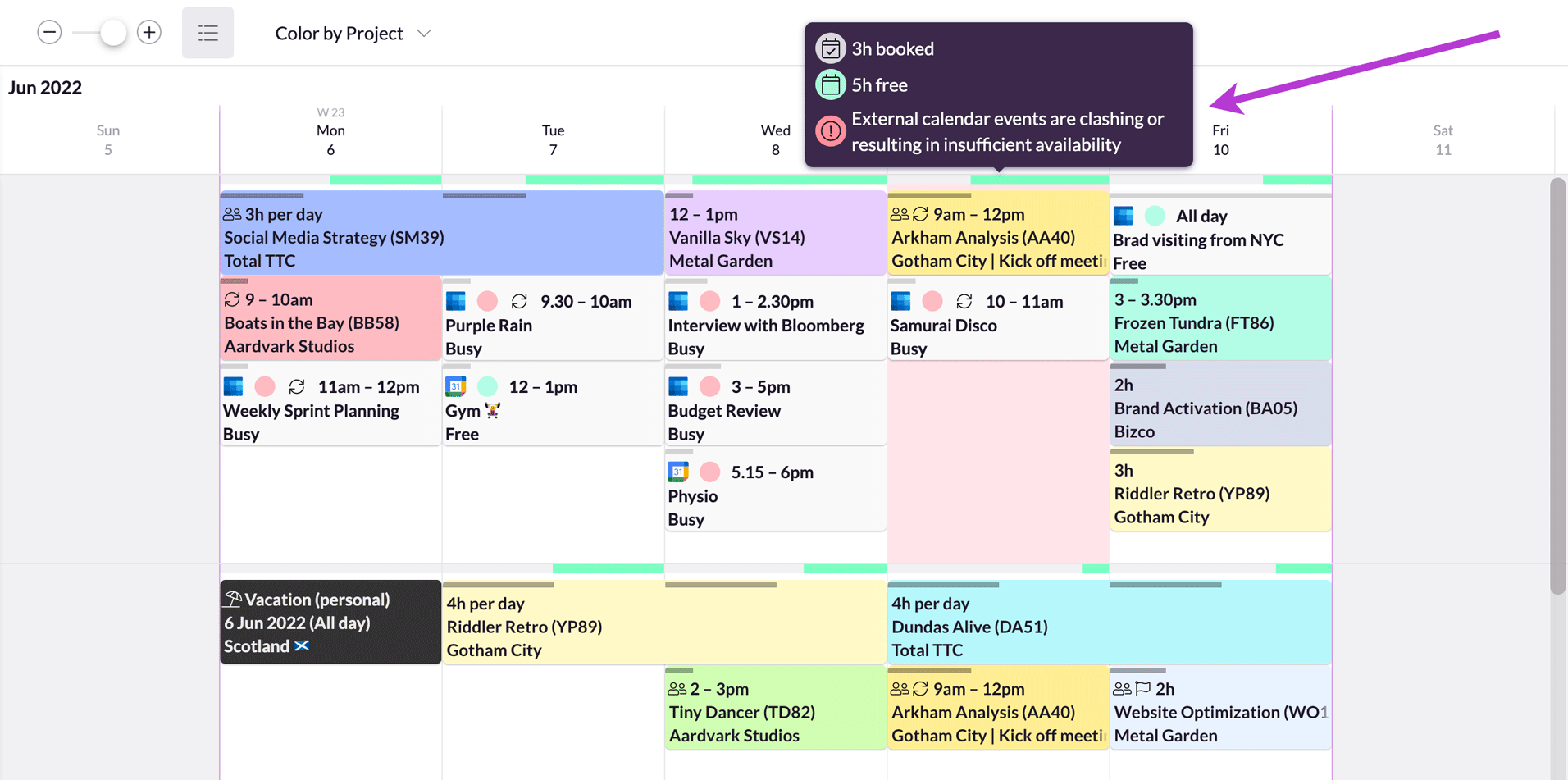
Most major calendar platforms – Google Calendar, Apple Calendar, and Outlook Calendar – offer a range of permission levels. Understanding these is the first step to sharing calendars securely. The common options are 'See only free/busy', 'See all event details', 'Make changes to events', and 'Manage sharing'.
"See only free/busy’ is the most restrictive. It allows someone to see when you’re available or busy, but not the specific details of your appointments. This is a good choice for colleagues you don"t need to share specifics with, or for broad availability sharing.
The 'See all event details' setting reveals titles, locations, and private notes. I only use this for immediate family or my direct assistant. The 'Make changes' level is even more intrusive, as it allows others to delete your appointments or move them without a notification. It is a full administrative hand-off, not just a helping hand.
That 'Make changes' permission can allow someone to completely disrupt your schedule if you aren’t careful. Finally, "Manage sharing" gives someone control over who else has access to your calendar. This is typically reserved for administrative assistants or trusted colleagues. It's a high-level permission that should be granted sparingly.
- See only free/busy covers availability only.
- See all event details: Full access to event information.
- Make changes to events: Add, edit, and delete events.
- Manage sharing: Control who else can access the calendar.
Privacy settings by platform
Let's look at how these permissions translate into practice on the most popular platforms. We’ll start with Google Calendar. To adjust default permissions, click the gear icon (Settings) > Settings > Share with specific people or groups. Here, you can set a default access level for anyone you add. You can also control whether new events are publicly visible by default.
In Apple Calendar, go to Calendar > Preferences > Sharing. You’ll see a list of calendars and the people you’ve shared them with. Click the 'Advanced' button for each shared calendar to adjust permissions. Apple's interface is less granular than Google's, but you can still control who can read and write to your calendar. It's particularly important to check the 'Public Calendar' setting to ensure your calendar isn’t accidentally visible to the world.
Microsoft Outlook Calendar requires a bit more navigation. In the desktop app, right-click on your calendar in the left pane and select 'Sharing Permissions'. You can then add users and assign them specific permissions. For Microsoft 365 users, there are also organization-wide sharing policies that an administrator can set. According to Microsoft’s documentation (learn.microsoft.com), administrators can share calendars with users outside their organization, but it requires careful configuration to maintain security.
Across all platforms, regularly review who has access to your calendar. Revoking access is usually straightforward – simply remove the person from the sharing list. Also, look for options to set expiration dates on shared access. This is a good practice for temporary collaborations.
- Google Calendar: Settings (gear icon) > Settings > Share with specific people or groups
- Apple Calendar: Calendar > Preferences > Sharing > Advanced
- Microsoft Outlook: Right-click calendar > Sharing Permissions
Sharing Links vs. Direct Invites: Which is Safer?
There are generally two ways to share a calendar: through a shareable link or by directly inviting individuals. Direct invites are almost always the safer option. When you invite someone directly, you have more control over their access. You know exactly who has access, and you can easily revoke it.
Shareable links, on the other hand, can be easily forwarded or shared with unintended recipients. If a link falls into the wrong hands, your calendar could be exposed to a wider audience than you intended. It’s surprisingly easy to make a calendar publicly visible with a link, even unintentionally.
The risk of link proliferation is significant. A single link can be copied and distributed countless times, making it difficult to track who has access. If you must use a shareable link, consider using a link management tool that allows you to track views and revoke access remotely. Always double-check the link settings to ensure it’s not set to "public".
Family Calendar Security: Protecting Young Schedules
Sharing calendars with family members presents unique challenges. While coordination is helpful, protecting the privacy of everyone involved – especially children – is paramount. Limiting access for younger children is crucial. They don’t need to see all the details of your schedule, and sharing too much information could put them at risk.
Consider creating separate calendars for different family groups. For example, a "Family’ calendar for shared events like appointments and vacations, and individual calendars for each family member’s personal commitments. This allows you to control what each person sees. Calendar Geek"s article on syncing family calendars offers further insights into managing these arrangements.
Be mindful of the information you include in shared events. Avoid including sensitive details like addresses or financial information. When inviting children to events, use appropriate permission levels – typically "See all event details’ is sufficient. Regularly review the calendar sharing settings to ensure they still align with your family"s needs.
Work Calendar Risks: Avoiding Data Leaks
Sharing work calendars carries its own set of security concerns. Your calendar can reveal confidential meetings, project timelines, and sensitive information about your company’s operations. Adhering to company policies regarding calendar sharing is essential.
Be cautious about sharing your calendar with external parties. If you must share it, ensure they understand the confidentiality of the information. Avoid including sensitive details in event titles or descriptions. Phishing attacks can also leverage calendar invites – be wary of suspicious meeting requests from unknown senders.
I’m not sure about the specifics of current attack vectors, but it’s generally a good practice to verify the sender’s identity before accepting any calendar invite. Regular security awareness training can help employees identify and avoid these threats. Always report any suspicious activity to your IT department.
Third-party app risks
Many of us use third-party apps that integrate with our calendars – scheduling tools like Calendly, productivity apps like Todoist, and even seemingly harmless browser extensions. These apps often require calendar access to function properly, but this access can pose a security risk.
It’s crucial to regularly review the permissions granted to these apps. Most calendar platforms allow you to see a list of connected apps and revoke their access. Read the fine print before granting any app calendar permissions. Understand what data the app will access and how it will be used.
Look for apps with a strong reputation and a clear privacy policy. Be especially wary of apps from unknown developers. If you’re no longer using an app, revoke its calendar access immediately. Identifying potentially malicious apps can be difficult, but red flags include excessive permission requests and a lack of transparency about data usage.


No comments yet. Be the first to share your thoughts!